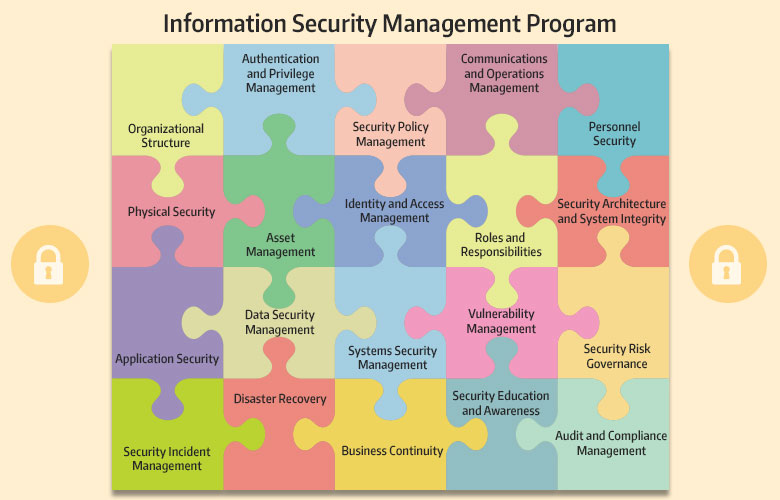
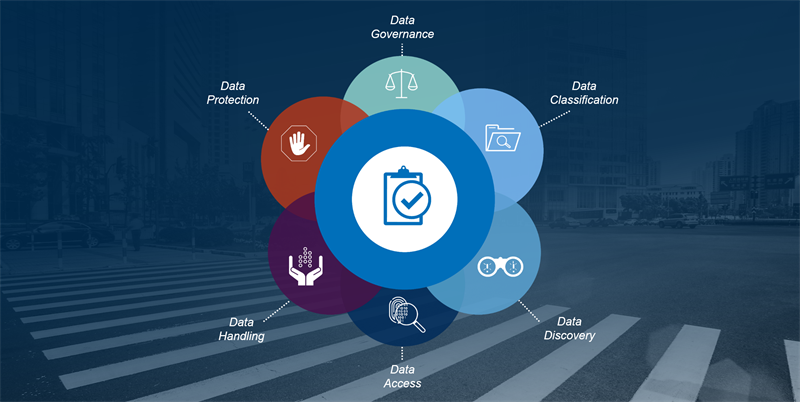
Security & Privacy By Design (SPBD) - Comprehensive cybersecurity for privacy by design program template and checklists
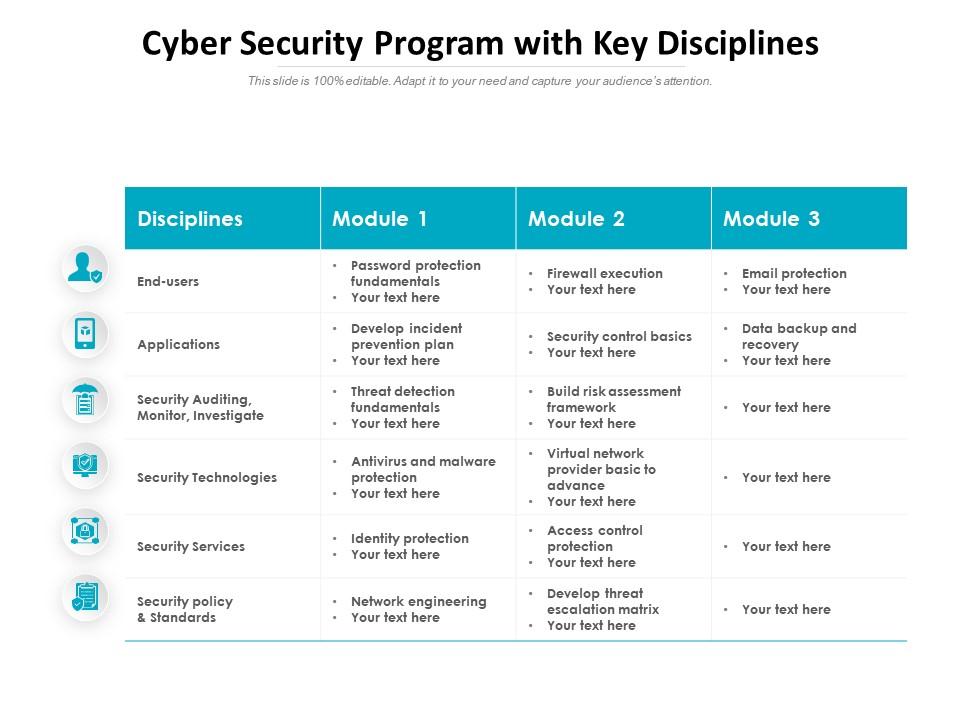
Cyber Security Program With Key Disciplines | Presentation Graphics | Presentation PowerPoint Example | Slide Templates

NYU Tandon Online on Twitter: "7 days left to the 11th #NYUCyberLecture! Find ways to use data science fundamentals in cyber security programs with us on October 6, 2021, at 1-2:30 pm